
Crypto accounts face increasingly sophisticated attacks in 2025, requiring multiple layers of protection
This guide outlines essential security steps to protect your crypto account from common threats. By implementing these measures, you’ll significantly reduce your risk of becoming another statistic in the growing list of crypto theft victims. Whether you’re a seasoned investor or just getting started with digital currencies, these security practices will help safeguard your valuable assets.
5 Critical Security Measures to Protect Your Crypto Account
Security Measure 1
Use Hardware Wallets for Cold Storage
Security Measure 2
Enable Two-Factor Authentication (2FA)
Security Measure 3
Protect Your Crypto from Phishing Scams
Security Measure 4
Practice Secure Password Management
Security Measure 5
Keep Software and Applications Updated Regularly
Use Hardware Wallets for Cold Storage
Hardware wallets represent the gold standard in cryptocurrency security. These physical devices store your private keys offline, completely isolated from internet-connected systems that are vulnerable to remote attacks.
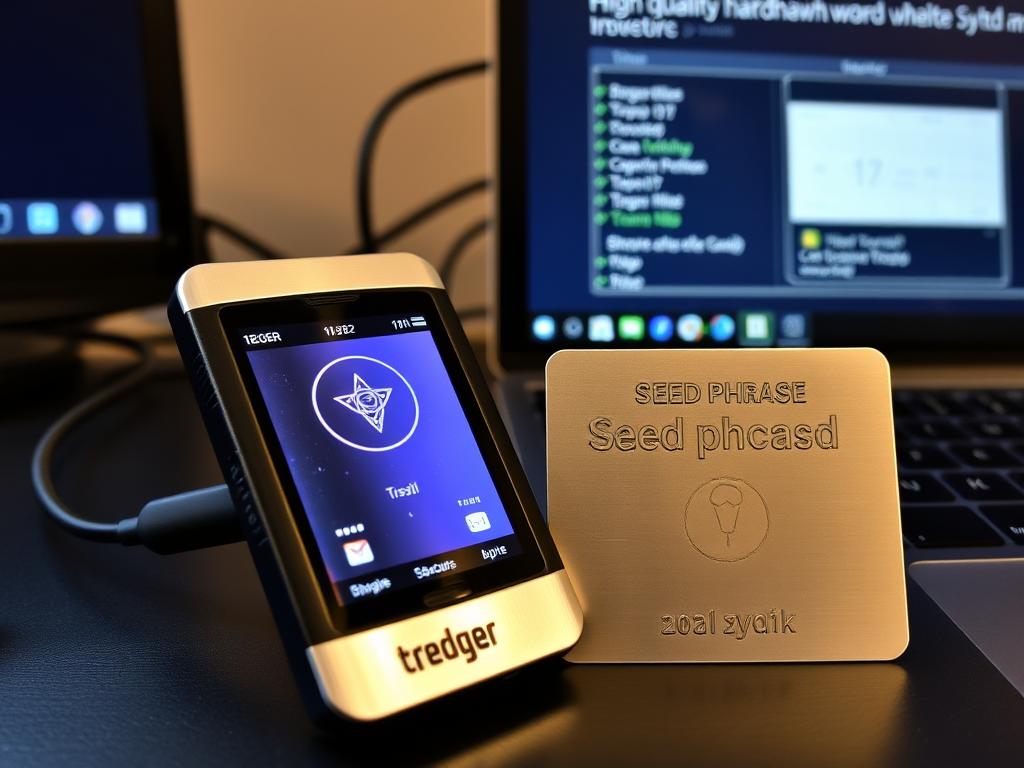
Why hardware wallets matter
When your private keys never touch an internet-connected device, they can’t be stolen through malware, phishing, or remote hacking attempts. This approach to using cold wallet storage creates an air-gap that hackers simply cannot breach remotely.
Store long-term holdings in cold storage
Only keep small amounts needed for regular tranOnly keep small amounts needed for regular transactions in hot walletssactions in hot wallets
Set up a strong PIN code
Protect against physical theft by requiring a PIN to access the device
Test recovery process
Verify you can restore your wallet before storing significant funds
Purchase hardware wallets directly from manufacturers
Avoid third-party resellers who might tamper with devices
Back up your seed phrase on metal
Paper backups can be damaged by water or fire; metal backups are more durable
By following these best practices, you can reduce the risk of losing your cryptocurrency to theft, damage, or technical failures.
Implementing strong security measures such as using a hardware wallet, storing your seed phrase on metal, and keeping your keys offline provides maximum protection for your digital assets. These steps not only guard against hackers and physical theft but also ensure your cryptocurrency remains safe from natural disasters and accidental loss.
Popular hardware wallet options include Ledger, Trezor, and KeepKey. These devices typically cost between $50-$200—a small price compared to the potential loss of your entire crypto portfolio.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds a critical second layer of security beyond your password. With 2FA enabled, accessing your account requires something you know (your password) and something you have (typically your phone).
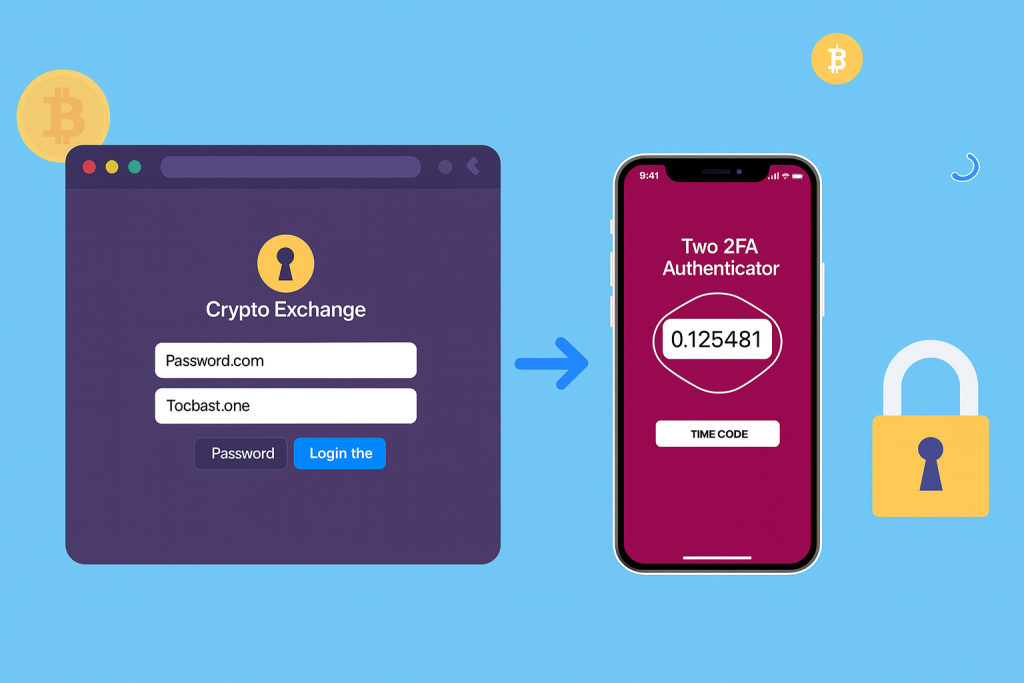
Important: Not all 2FA methods offer equal protection. Authenticator apps provide significantly better security than SMS-based verification, which is vulnerable to SIM-swapping attacks.
Hardware security keys (YubiKey, Titan)
Physical devices that connect to your computer or phone
Authenticator apps (Google Authenticator, Authy
Generate time-based codes on your device
Email accounts
Especially those linked to your crypto accounts
Email verification
Sends codes to your email (ensure your email is also secured with 2FA)
Cryptocurrency exchanges
Whitebit,Mexc,bitget, Binance, Kraken, etc.
Web wallets
MetaMask, Trust Wallet (when available)
Cloud storage
If you store any wallet backups digitally
Password managers
Protect access to all your stored passwords
When setting up 2FA, always save backup codes in a secure location. If you lose your authentication device, these codes will be your only way to regain account access.
Avoid Phishing Scams: Red Flags to Watch For
Phishing remains one of the most common ways crypto accounts are compromised. These attacks trick you into revealing your private keys, seed phrases, or login credentials by impersonating legitimate services.

Essential Password Security Rules:
Use a different password for each crypto service
If one site is breached, others remain secure
Create long, complex passwords
Aim for at least 16 characters with mixed case, numbers, and symbols
Employ a password manager
Tools like Bitwarden, 1Password, or LastPass generate and store strong passwords
Never store passwords in plain text
Don’t keep them in notes apps, documents, or email
Avoid personal information
Don’t use names, birthdays, or other easily guessable information
Change passwords periodically
Update credentials every 3-6 months for critical accounts help convince the visitor that you are a good fit for them.
What to Keep Updated:
Many crypto users delay updates out of convenience or fear of changes to the interface. However, these updates often contain patches for critical security vulnerabilities that could put your assets at risk.Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Pro Tip

Multi-Signature helps you complete transactions from a multisig account.
Beyond the essential security measures, these advanced strategies provide additional layers of protection for users with significant crypto holdings or those seeking maximum security.

Multi-Signature helps you complete transactions from a multisig account.
Multi-signature (multisig) wallets require multiple private keys to authorize transactions, similar to a bank vault requiring several keys to open. This approach prevents a single point of failure in your security setup.
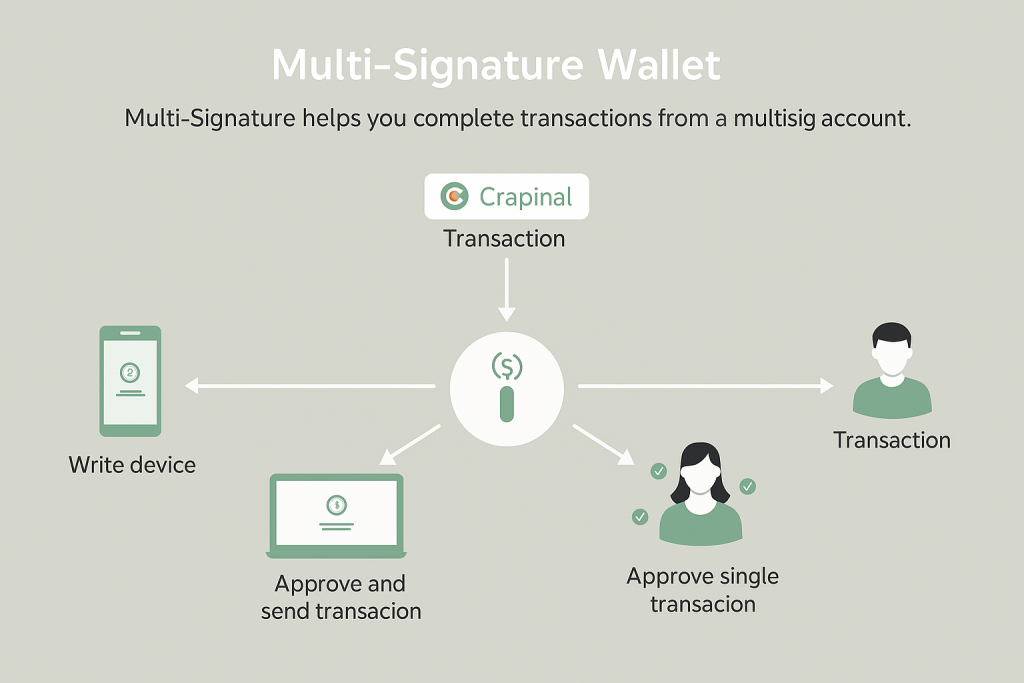
Multi-signature wallet transaction requiring multiple approvals
Benefits of Multi-Signature Wallets:
_Protection against single device compromise – Even if one key is stolen, funds remain secure
_Shared custody options – Ideal for business accounts or family holdings
_Inheritance planning – Can be configured to allow heirs access under specific conditions
_Reduced risk of theft – Attackers would need to compromise multiple devices or individuals
Popular multisig implementations include Electrum for Bitcoin, Gnosis Safe for Ethereum and EVM-compatible chains, and native multisig support on platforms like Blockstream’s Liquid.
Use a VPN for Enhanced Privacy
A Virtual Private Network (VPN) encrypts your internet connection, hiding your IP address and making it more difficult for attackers to monitor your crypto activities or target you specifically.

When Using a VPN for Crypto:
_Choose a reputable, no-logs VPN provider – Research their privacy policy and jurisdiction
_Enable the kill switch feature – Prevents data leakage if the VPN connection drops
_Use VPN when accessing exchanges or wallets – Especially on mobile devices
_Be aware that some exchanges flag VPN usage – May require additional verification steps
A VPN adds an important layer of privacy, but remember it doesn’t make you completely anonymous. Always combine it with other security practices for comprehensive protection.
Avoid Public Wi-Fi for Crypto Transactions
Public Wi-Fi networks present significant security risks for crypto users. These networks are often unencrypted and vulnerable to various attacks that could compromise your sensitive information.

Dangers of using public WiFi for crypto transactions
Risks of Public Wi-Fi:
_Man-in-the-middle attacks – Attackers intercept communication between you and legitimate services.
_Evil twin networks – Fake networks that mimic legitimate ones to steal information
_Packet sniffing – Capturing data transmitted over the network
_Session hijacking – Taking over authenticated sessions to gain unauthorized access
Safe Alternatives: Use your mobile data connection, a personal hotspot, or a home network with a strong password when accessing crypto accounts. If you must use public Wi-Fi, always connect through a VPN firs
Even with a VPN, it’s best to avoid making transactions or accessing sensitive accounts on public networks altogether. Save these activities for trusted, secure connections.
Implement Device Segregation
For maximum security, consider using dedicated devices specifically for crypto transactions. This approach isolates your crypto activities from potentially vulnerable everyday computing environments.

Dedicated crypto computer separated from everyday devices
Device Segregation Strategies:
_Dedicated crypto computer – A separate laptop used only for managing digital assets
_Air-gapped systems – Computers that are never connected to the internet
_Clean operating system – Fresh installation with minimal software to reduce attack surface
_Mobile segregation – Separate phone or tablet for crypto apps only
While this approach requires additional investment and effort, it provides significant security benefits for those with substantial crypto holdings by minimizing exposure to malware and other threats.
Comprehensive Crypto Security Checklist

-
Essential Security Measures:
Administrator
-
☐ Use hardware wallet for long-term storage
-
☐ Enable 2FA on all crypto-related accounts
-
☐ Create unique, strong passwords for each service
-
☐ Implement a password manager
-
☐ Keep all software and apps updated
-
☐ Bookmark official websites to avoid phishing
-
☐ Back up seed phrases securely (preferably on metal)
-
Advanced Security Measures:
Administrator
-
☐ Set up multi-signature wallet for high-value holdings
-
☐ Use a reputable VPN when accessing crypto accounts
-
☐ Avoid public Wi-Fi for transactions
-
☐ Consider device segregation for crypto activities
-
☐ Enable email alerts for account activities
-
☐ Enable email alerts for account activities
-
☐ Create a crypto inheritance plan
Remember that crypto security is not a one-time setup but an ongoing process. Regularly review and update your security practices as new threats emerge and better protection methods become available.
Common Crypto Security Mistakes to Avoid
Even experienced crypto users sometimes make security mistakes that put their assets at risk. Being aware of these common pitfalls can help you avoid potentially costly errors.

Common crypto security mistakes illustrated with warning symbols
Security Mistakes That Put Your Crypto at Risk
Storing seed phrases digitally – Screenshots, cloud documents, or email are all vulnerable to hacking
Using the same password across multiple platforms – Creates a single point of failure
Keeping large amounts in exchange wallets – Exchanges can be hacked or become insolvent
Sharing private keys or seed phrases – No legitimate service will ever ask for these
Neglecting 2FA – Passwords alone are insufficient protection
Falling for “too good to be true” offers – Giveaways promising to double your crypto are always scams
Clicking links in unsolicited emails or messages – Primary vector for phishing attacks
Ignoring software updates – Leaves known vulnerabilities unpatched
What to Do If Your Crypto Account Is Compromised
Despite your best efforts, security breaches can still occur. Knowing how to respond quickly can potentially limit the damage if your crypto account is compromised.
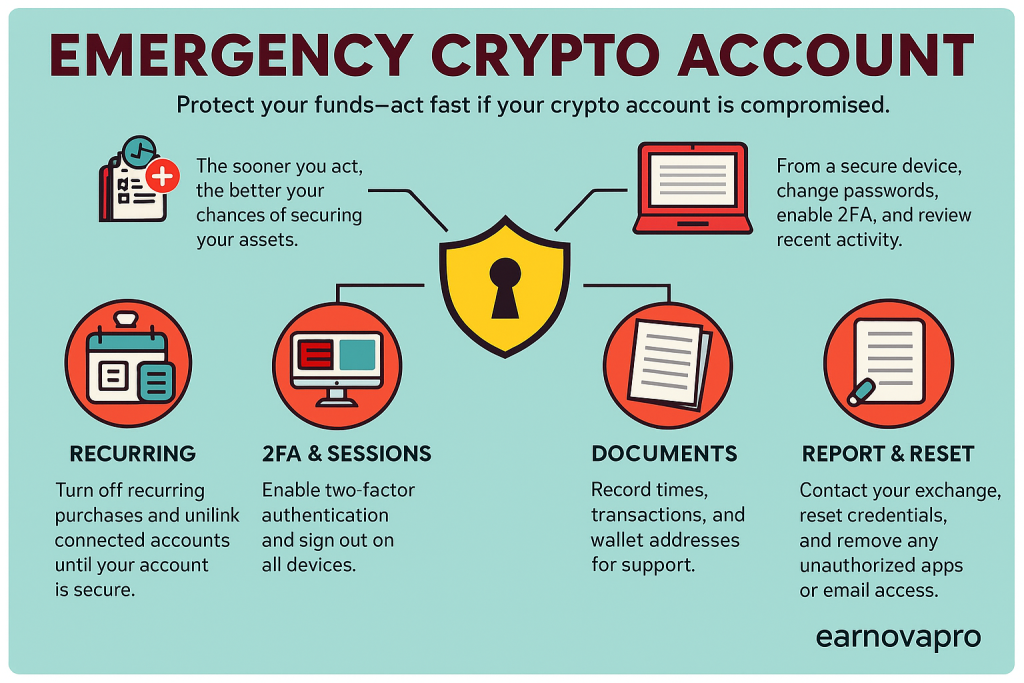
“Emergency steps to secure a compromised crypto account.”
Immediate Actions to Take:
1_Secure your remaining accounts – Change passwords and 2FA on any uncompromised accounts immediately
2_Transfer funds from vulnerable wallets – If you still have access, move assets to secure wallets
3_Contact the exchange or wallet provider – Report the incident and follow their security protocols
4_Document everything – Record transaction IDs, timestamps, and any suspicious activities
5_File a police report – While recovery is unlikely, documentation is important for insurance or tax purposes
6_Check connected services – Revoke access for any third-party apps or services
Important: Be extremely cautious of recovery services that claim they can retrieve stolen crypto. Many of these are secondary scams targeting victims who are already vulnerable. Legitimate blockchain forensics companies exist but typically work with law enforcement rather than directly with individuals.
After addressing the immediate situation, take time to analyze how the breach occurred and strengthen your security practices to prevent similar incidents in the future.
Conclusion: Your Crypto Security Journey
Protecting your crypto account requires vigilance, education, and the implementation of multiple security layers. While no security system is completely impenetrable, following the practices outlined in this guide will significantly reduce your risk of becoming a victim of crypto theft.

Secure crypto setup with multiple security layers implemented
Remember that crypto security is not a one-time setup but an ongoing process. As the technology evolves and new threats emerge, continue to educate yourself and adapt your security practices accordingly. The time and effort invested in securing your digital assets is minimal compared to the potential losses from a security breach.
Start implementing these security measures today—beginning with the most critical steps like using hardware wallets and enabling two-factor authentication. Then gradually enhance your security posture with the more advanced techniques as you become comfortable with the basics.
Share Your Crypto Security Tips
Do you have additional security practices that have worked well for you? Share your experiences and help build a more secure crypto community. Your insights could help others protect their digital assets.
Disclaimer: This article is for educational purposes only. Always conduct independent research and consider consulting with a security professional for personalized advice on protecting your crypto assets.
Frequently Asked Questions About Crypto Security
What is the difference between hot wallets and cold wallets?
Are cryptocurrency exchanges safe for storing crypto?
What should I do if I lose my seed phrase?
Have you created detailed instructions for your heirs on how to access your crypto?
Is it safe to use mobile wallets for crypto?
Mobile wallets can be reasonably secure if used properly, but they have inherent limitations:
Mobile Wallet Advantages (Yes)
- Convenient for everyday transactions
- Many support biometric authentication
- Easier to use than hardware wallets
- Often include built-in exchange features
Mobile Wallet Risks (No)
- Phones can be lost, stolen, or compromised
- Malware specifically targets crypto apps
- Connected to the internet (hot wallet)
- App store scams with fake wallet apps
For better mobile wallet security: only download from official sources, keep your device updated, enable all security features, and don’t store large amounts in mobile wallets.
